Top 5 Host-Based Intrusion Detection Systems in Canada, 2026
Published on Thursday, January 1, 2026
Host-Based Intrusion Detection Systems (HIDS) are specialized security solutions that operate on individual devices, meticulously monitoring system calls and file activities to detect any unauthorized access or malicious behavior. As organizations in Canada face increasing cybersecurity threats, HIDS have become a non-negotiable aspect of their defensive strategy. Their capability to provide real-time monitoring and immediate alerts significantly appeals to Canadian businesses that prioritize data security. As cyberattacks grow more sophisticated, the importance of implementing a robust HIDS cannot be overstated, ensuring that every device connected to the network is continuously protected from both internal and external threats.
Top Picks Summary
Their in-depth monitoring capabilities enable them to detect internal threats that may bypass network security, ensuring comprehensive protection at every endpoint.
Understanding Host-Based Intrusion Detection Systems
Host-Based Intrusion Detection Systems (HIDS) play a crucial role in enhancing organizational security by focusing on individual devices. By monitoring and analyzing activities for any signs of tampering or malicious intent, HIDS provide a layer of defense against increasingly sophisticated cyber threats.
Real-time Monitoring: HIDS actively observes system activities, allowing for immediate detection of suspicious behavior and rapid response.
Internal Threat Detection: Unlike traditional network security solutions, HIDS specifically monitors the endpoints, ensuring that threats originating internally are swiftly identified.
Enhanced Compliance: Many industries require stringent data protection measures; implementing HIDS helps organizations meet compliance standards effectively.
Integration with Existing Systems: HIDS can typically be incorporated with existing IT infrastructures, providing security without major disruptions.
Automated Alerts: Users receive prompt alerts about potential issues, allowing for faster incident response strategies and minimizing damage.
Data Integrity Verification: Regular checks on file changes help maintain data integrity and notify administrators of unauthorized alterations.
Frequently Asked Questions
Which HIDS should I choose for Canadian teams using EDR?
Choose CrowdStrike Falcon Insight: it’s an endpoint detection and response solution with real-time threat intelligence, advanced EDR capabilities, and a cloud-native architecture, with an average rating of 4.8.
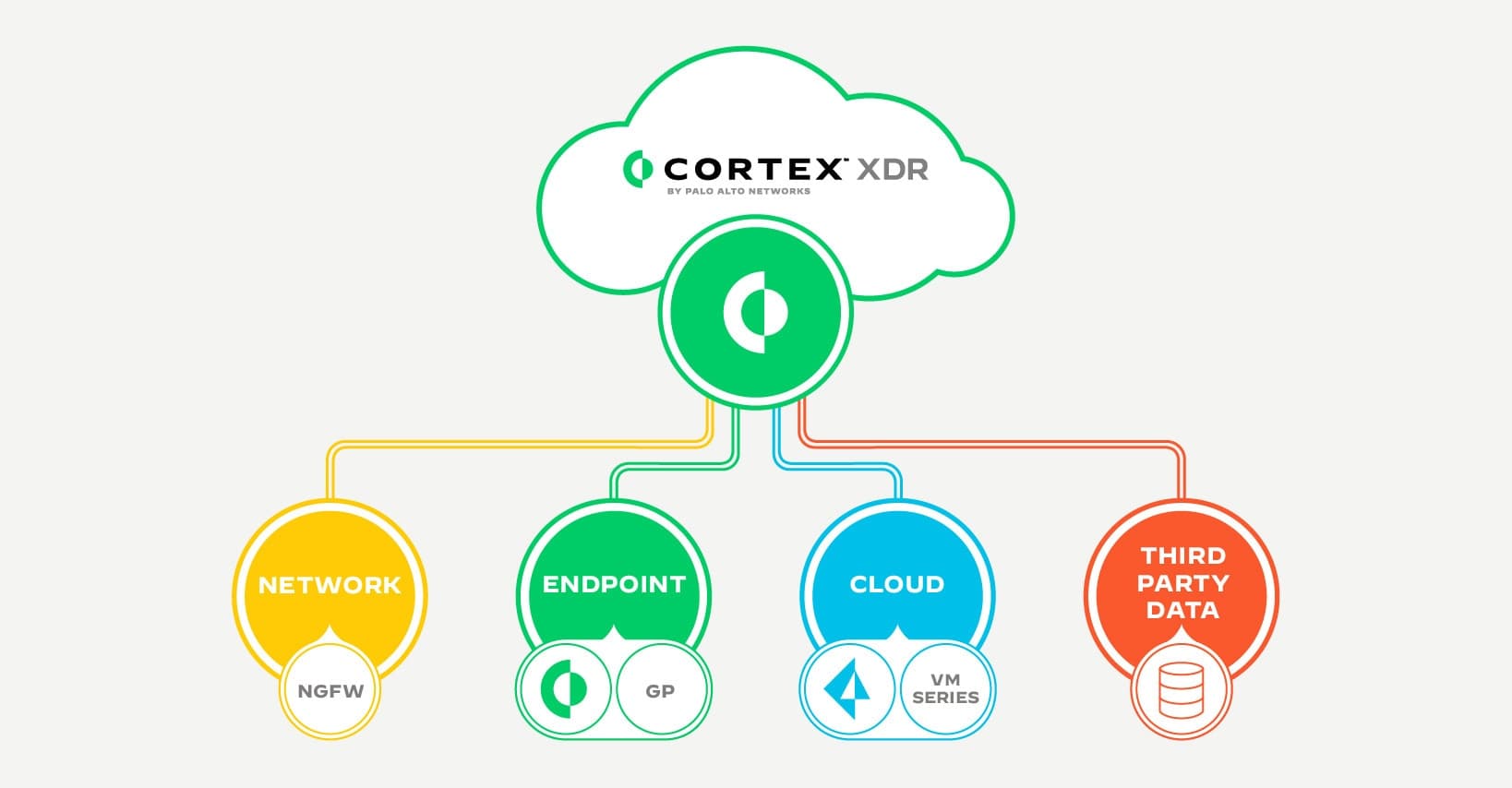
What feature does Palo Alto Networks Cortex XDR provide?
Palo Alto Networks Cortex XDR provides unified threat detection and response, plus seamless integration with Palo Alto firewall and robust analytics capabilities, with an average rating of 4.6.
How does CrowdStrike Falcon Insight pricing compare in Canada?
The provided data doesn’t include any Canadian pricing for CrowdStrike Falcon Insight, so I can’t compare price-to-value; it’s rated 4.8 and includes real-time threat intelligence, advanced EDR, and a cloud-native architecture.
Does Cisco Secure Endpoint include integration with Cisco network?
Cisco Secure Endpoint includes integration with Cisco secure network, has a user-friendly management interface, and provides comprehensive endpoint protection; it’s rated 4.5, and no warranty duration is listed in the provided data.
Conclusion
In conclusion, as cybersecurity threats continue to evolve in 2026, selecting a top-tier Host-Based Intrusion Detection System is crucial for Canadian businesses. We hope you found this guide on HIDS helpful, and encourage you to search for more specific queries using the search bar to enhance your cybersecurity strategy.